Certifikatovervågning &
Compliance Management
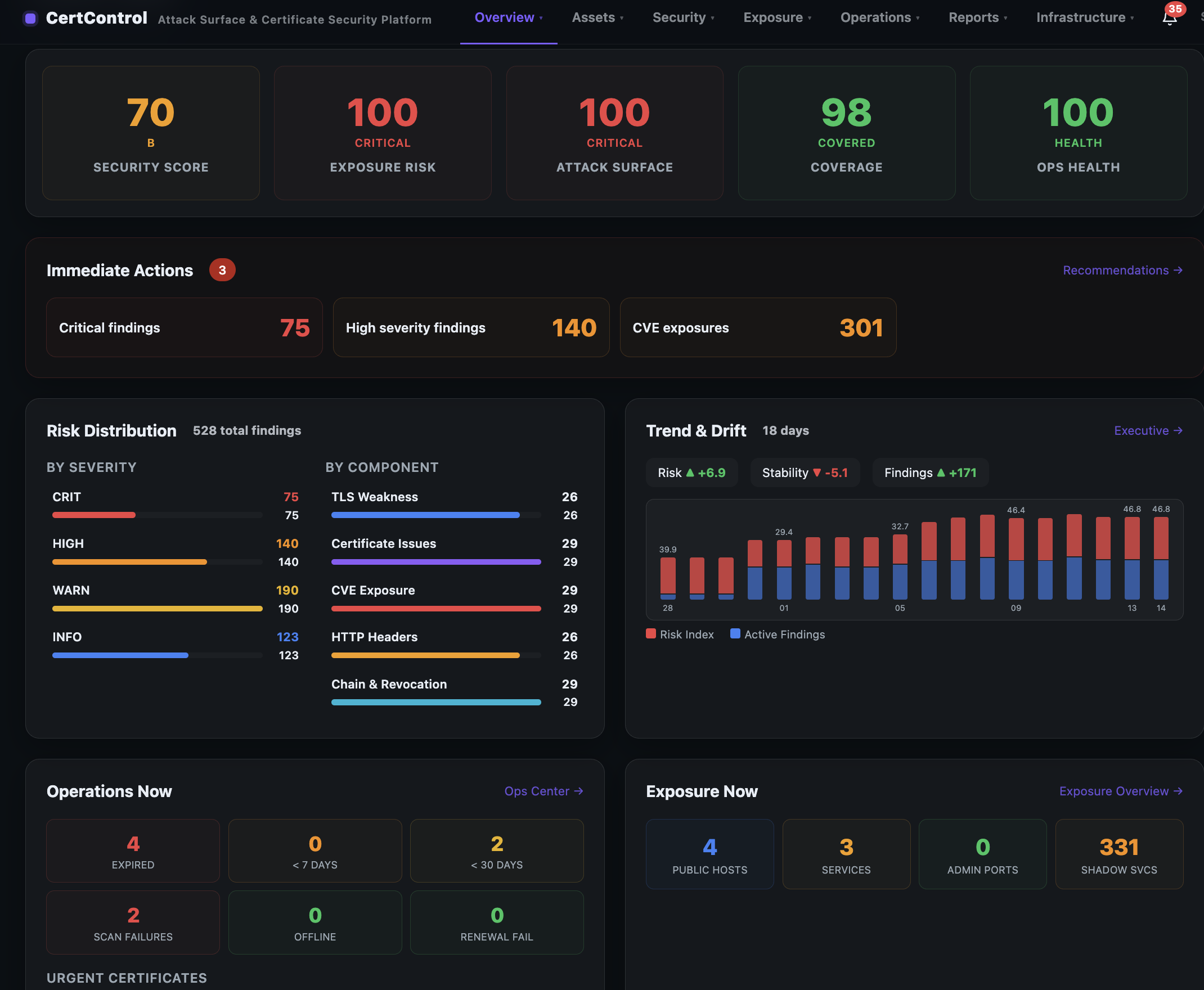
Én platform for certifikat-livscyklusstyring, TLS-sikkerhedsanalyse, attack surface visibility og compliance-rapportering — bygget til drifts- og sikkerhedsteams.
14-day free trial · Dedicated instance · EU hosted
Alt du behøver — i én platform
From real-time certificate tracking to attack path visualization. Built as one system, not five disconnected tools.
Certificate lifecycle management
Track every certificate — expiry, chain health, revocation (OCSP), SAN validation, risk scoring and ownership across all environments (prod, pilot, test, dev).
TLS & HTTP security analysis
Detect weak protocols (TLS 1.0/1.1), deprecated ciphers, and missing security headers (HSTS, CSP, X-Frame-Options). Full A+ to F grading per endpoint.
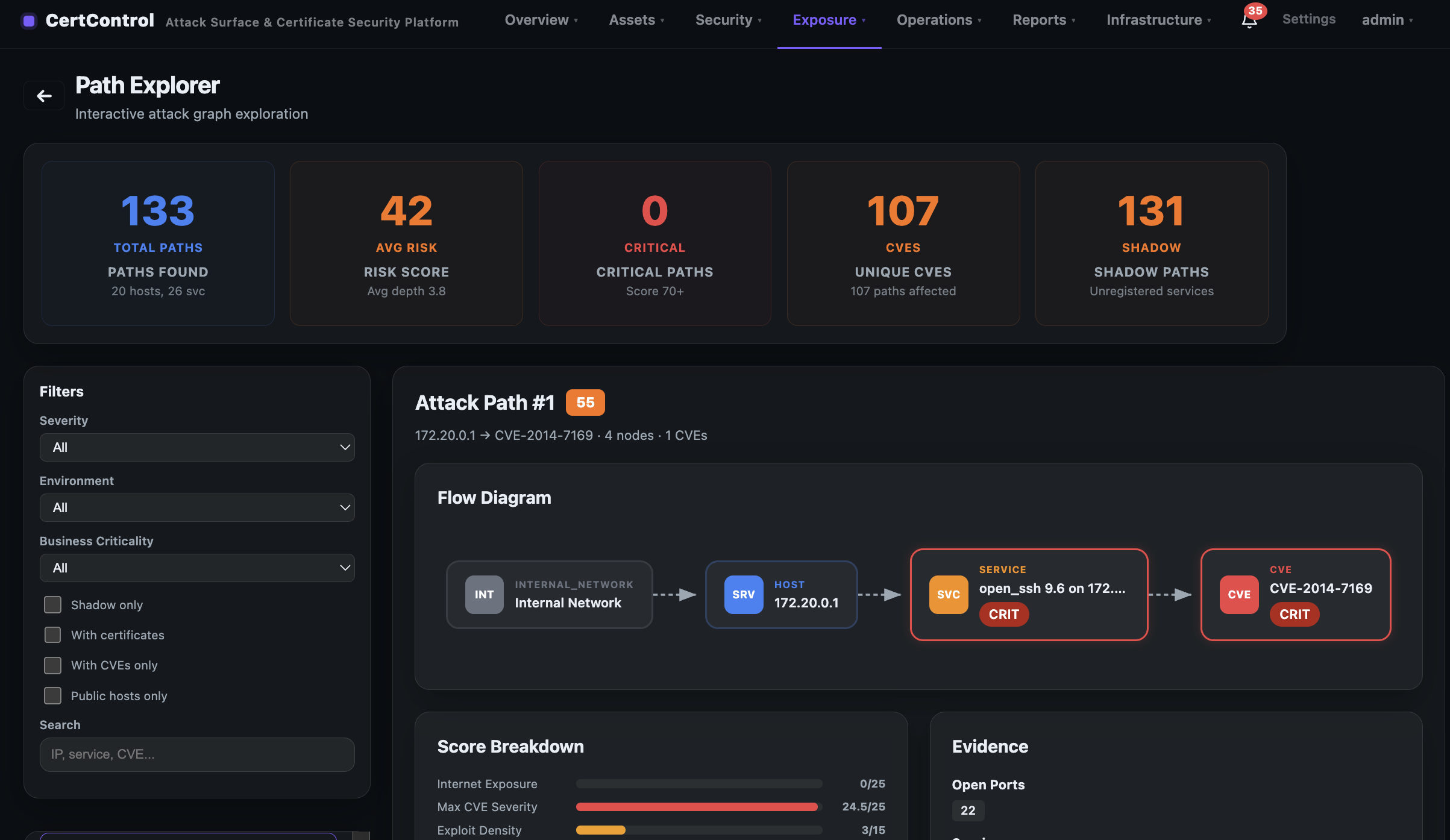
Attack path visualization
See how CVEs, shadow assets, and open ports connect into exploitable paths from internet to critical systems. Top 50 ranked paths with evidence.
Executive reporting
Four professional report types: Executive Summary, Operational Risk, Expiry Forecast, and Change/Drift detection — print-ready for the board and audits.
ACME / Let's Encrypt automation
Automated issuance and renewal via HTTP-01 or DNS-01 challenges. Private keys encrypted at rest with AES-256-GCM. Removes the manual burden entirely.
On-premise scanning agent
Lightweight Docker agent scans internal networks behind your firewall. Outbound HTTPS only — no inbound ports, no VPN, no remote execution.
Hvert overblik du behøver — indbygget
From real-time scanner operations to board-ready executive reports.
Bygget anderledes — med vilje
Enterprise-grade capabilities at a price that makes sense. No shared tenants, no legacy architecture, no compromise.
Din egen dedikerede instans
Every customer gets a fully isolated Docker environment with a separate database and network. Your data is never co-mingled.
Bygget i Danmark, hostet i Europa
A Danish company with all infrastructure in EU data centres. Full GDPR alignment, standard DPA available for all paid plans.
Specialfunktioner, leveret hurtigt
No six-month roadmap. No enterprise sales cycle. Tell us what you need — we build and ship quickly to match your operational reality.
Vi praktiserer hvad vi prædiker
Security is not a feature added later. It's built into every line of code from day one.
Scan interne netværk uden at åbne firewalls
Cloud-only tools miss internal assets. CertControl deploys a lightweight Docker agent behind your firewall — it scans locally and pushes only metadata outbound.
Zero Trust
Outbound HTTPS only. No inbound ports, no VPN, no remote execution.
Privacy by Design
Internal hostnames replaced with [masked] before data leaves your network.
~200 MB Docker image
Alpine-based, non-root. Runs anywhere Docker runs. No database.
Offline resilient
Local disk spool queues results when cloud is unreachable. Never lose scan data.
How the agent works
Your internal network
TLS scan · OCSP check · HTTP headers · Service fingerprint · Hostname redaction
CertControl Cloud
Unified dashboard · Security scoring · Expiry alerts · Push config to agents
Bygget af folk der har haft vagttelefon
CertControl is designed by engineers who have experienced certificate-related outages firsthand — when login flows break and the board asks how it happened.
Identity & Access Management
Deep expertise in OIDC, SAML, and OAuth2. We understand how certificates underpin authentication flows and what breaks when they expire unexpectedly.
Kubernetes & Cloud Platforms
Hands-on experience with container orchestration and cloud-native architectures — and the certificate complexity they introduce at scale.
Reverse Proxies & Edge Security
Experience with F5, ISVA, and other reverse proxies — where certificate misconfigurations cause the most visible and painful outages.
Enterprise Operations & Compliance
We know audit and governance requirements firsthand. CertControl is built to satisfy them — not as an afterthought, but from the ground up.
Klar til at se den fulde platform?
Start your 14-day free trial with full access, or book a guided demo with our team.