NIS2 (Directive EU 2022/2555) entered into force in January 2023 and required member state transposition by October 2024. It significantly expands the scope of its predecessor — moving from a narrow set of operators of essential services to a broader framework covering essential and important entities across 18 sectors, with stricter security requirements and meaningful enforcement mechanisms including personal liability for senior management.
NIS2 Article 21 is more specific than most compliance frameworks: it enumerates the security measures covered entities must implement, several of which map directly to certificate and PKI management.
The NIS2 requirements most relevant to certificates
Article 21(2)(a) — Policies on risk analysis and information system security. NIS2 requires documented risk analysis covering information systems. TLS certificates are critical infrastructure components — expired or compromised certificates represent concrete, quantifiable operational and security risk. A risk analysis that does not account for certificate lifecycle is incomplete under this requirement.
Article 21(2)(b) — Incident handling. NIS2 requires defined incident handling procedures. Certificate expiry that causes service outages is an incident. A compromised private key that enables traffic interception is a security incident with potential data breach implications. Without a certificate inventory, responding to a certificate-related incident requires first figuring out what certificates exist and where they are used — adding significant time to incident response when time matters most. A disciplined approach to certificate lifecycle management closes that gap before an incident occurs.
Article 21(2)(e) — Security in network and information systems acquisition, development and maintenance, including vulnerability handling and disclosure. This includes the use of encryption and PKI. An expired certificate is a direct failure under this sub-article — there is no grey area. This sub-article alone gives supervisory authorities grounds to cite certificate management as a security deficiency.
Article 21(2)(h) — Policies and procedures regarding the use of cryptography and, where appropriate, encryption. This is the sub-article most directly applicable to TLS certificates. Maintaining valid certificates with strong key sizes, modern cipher suites, and SHA-256 signatures is a direct implementation of the cryptography policy requirement. An organisation that cannot demonstrate controlled, documented certificate management has a gap here that auditors will probe.
Supply chain provisions (Article 21(2)(d) and Article 22). NIS2 places significant emphasis on supply chain security. Under Article 22, organisations must actively manage third-party cybersecurity risk — not simply assume suppliers are compliant. A supplier whose TLS certificate expires creates a disruption that is your incident to report if it affects services your organisation depends on. See how monitoring third-party TLS certificates gives you visibility before incidents occur.
The reporting dimension
NIS2 introduces mandatory incident reporting with short timelines: early warning within 24 hours, incident notification within 72 hours, and a final report within one month for significant incidents. A certificate expiry causing service unavailability or a compromised certificate enabling a breach can both qualify as significant incidents requiring notification to national authorities. The NIS2 guide covers the full scope of obligations for covered organisations.
The 24-hour early warning requirement is particularly demanding. It assumes that when an incident occurs, the organisation has the information needed to report quickly — including understanding which systems are affected and what the impact scope is. Without a certificate inventory, establishing that a certificate expiry is the root cause and understanding what systems it affects can itself take hours.
What NIS2-ready certificate management looks like
With NIS2 supervisory frameworks now active across EU member states, the baseline for certificate management has shifted. These are the capabilities that directly address what supervisory authorities will examine:
A complete, current asset inventory. Every certificate in use across the organisation's information systems should be in a managed TLS certificate inventory with expiry dates, owners, environments, and associated systems documented. This is the foundation for risk analysis, incident response, and demonstrating compliance to supervisory authorities.
Documented risk assessment for certificate lifecycle. The risk analysis required by Article 21(2)(a) should explicitly address certificate expiry risk, certificate compromise risk, and the organisation's controls and residual risk. This needs to be a living document, not a one-time exercise.
Defined incident response procedures for certificate events. What happens when a certificate expires unexpectedly? What happens if a private key compromise is suspected? Who is notified? Who makes the decision to revoke? What is the escalation path? These procedures should be documented and tested.
Supplier certificate monitoring. If your suppliers provide services over TLS, their certificate health is part of your supply chain security posture. Monitoring key supplier certificates for expiry and configuration issues provides early warning of third-party disruptions.
Audit-ready reporting. Supervisory authorities under NIS2 have significant powers to request information and conduct inspections. Certificate inventory reports, expiry forecasts, and historical incident records must be producible on demand. Documentation assembled retroactively answers only the question of today — not the past six months. Our guide to NIS2 documentation for the CISO and the certificate audit checklist set out exactly what to keep on hand. See how CertControl supports audit-ready certificate management and the NIS2 compliance checklist.
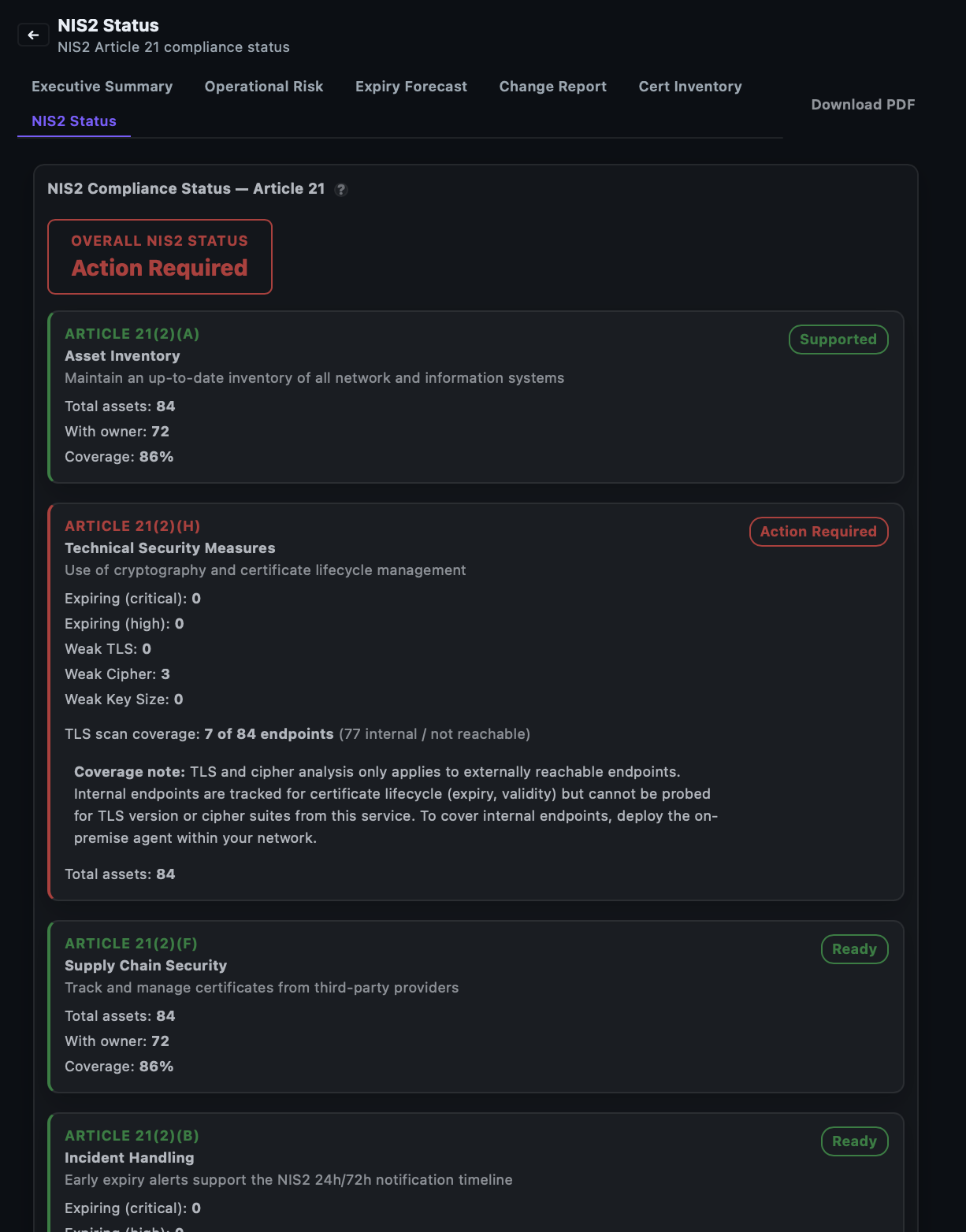
How CertControl addresses NIS2 requirements
CertControl provides the certificate inventory, monitoring, and reporting capabilities that NIS2-covered organisations need. The platform maintains a continuous, automatically updated inventory of all certificates across monitored endpoints — internal and external — with expiry tracking, TLS configuration assessment, and clear ownership assignment.
Executive and operational reports are built into the platform, covering certificate status, expiry forecasts, compliance scores, and drift detection — providing the audit-ready documentation that NIS2 supervisory oversight may require. Configurable alerts with long lead times ensure that certificate expiry approaching critical thresholds reaches the right people with enough time to act within any change management constraints.
Supplier certificate monitoring extends the same inventory and alerting to third-party services — covering the supply chain dimension of NIS2 without requiring manual tracking processes that cannot scale.
Frequently asked questions
Which NIS2 article applies most directly to TLS certificates?
Article 21(2)(h) on policies and procedures regarding the use of cryptography is the most directly applicable. Maintaining valid certificates with strong key sizes, modern cipher suites, and SHA-256 signatures is a direct implementation of that cryptography policy requirement.
Is an expired certificate a NIS2 incident?
Yes. A certificate expiry that causes a service outage is an incident under Article 21(2)(b), and if it affects an essential service it can qualify as a significant incident requiring notification to national authorities. A compromised private key enabling traffic interception is a security incident with potential data breach implications.
What are the NIS2 incident reporting timelines?
NIS2 requires an early warning within 24 hours, an incident notification within 72 hours, and a final report within one month for significant incidents. The 24-hour early warning assumes the organisation can quickly identify affected systems, which is difficult without a certificate inventory.
Are suppliers' certificates my responsibility under NIS2?
Under Article 22 and Article 21(2)(d), organisations must actively manage third-party cybersecurity risk rather than assume suppliers are compliant. A supplier whose TLS certificate expires creates a disruption that is your incident to report if it affects services your organisation depends on.
What documentation do NIS2 supervisory authorities expect?
Authorities can request information and conduct inspections, so certificate inventory reports, expiry forecasts, and historical incident records must be producible on demand. Documentation assembled retroactively only answers the question of today, not the past six months, so a continuous record is far more credible.
