Does NIS2 apply to certificates and TLS?
Yes. NIS2 Article 21(2)(h) requires securing the acquisition, development, and maintenance of information systems — including TLS/PKI. Expired or misconfigured certificates count as a technical security weakness under the directive. Supervisory authorities are expected to request documentation of certificate management processes during inspections.
When does a certificate expiry become a NIS2 incident?
A certificate expiry causing service unavailability, inaccessibility of critical systems, or a data breach can qualify as a significant incident under NIS2. The assessment depends on the criticality of the system and the scope of impact. The definition of "significant incident" is broadly worded — and uncertainty should always lead to reporting.
Which organisations are in scope for NIS2?
NIS2 covers essential and important entities across 18 sectors including energy, transport, banking, healthcare, digital infrastructure, and public administration. Generally, organisations with 50 or more employees or annual revenue exceeding €10 million operating in a covered sector are in scope. Member states may apply the directive more broadly to certain categories.
What are the penalties for NIS2 non-compliance?
Important entities can be fined up to €7 million or 1.4% of global annual turnover. Essential entities can be fined up to €10 million or 2% of global annual turnover. In addition, senior management can be held personally liable for failures to implement adequate security measures.
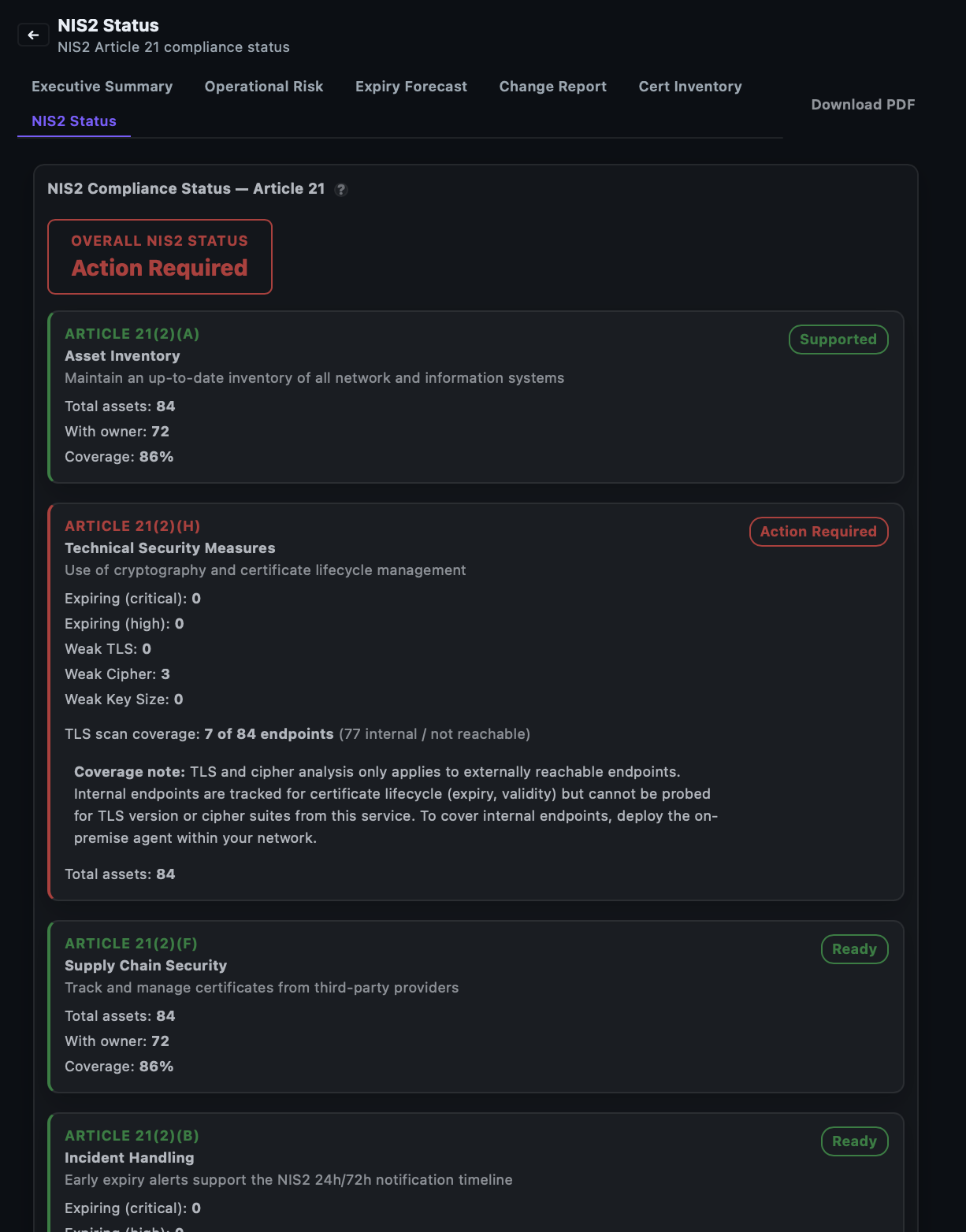
Can CertControl generate documentation for NIS2 supervisory inspections?
Yes. CertControl generates executive and operational reports with complete certificate status, expiry forecasts, compliance scores, and historical incident records. The reports are designed to be presented directly to supervisory authorities or management — downloadable in one click without manual assembly.